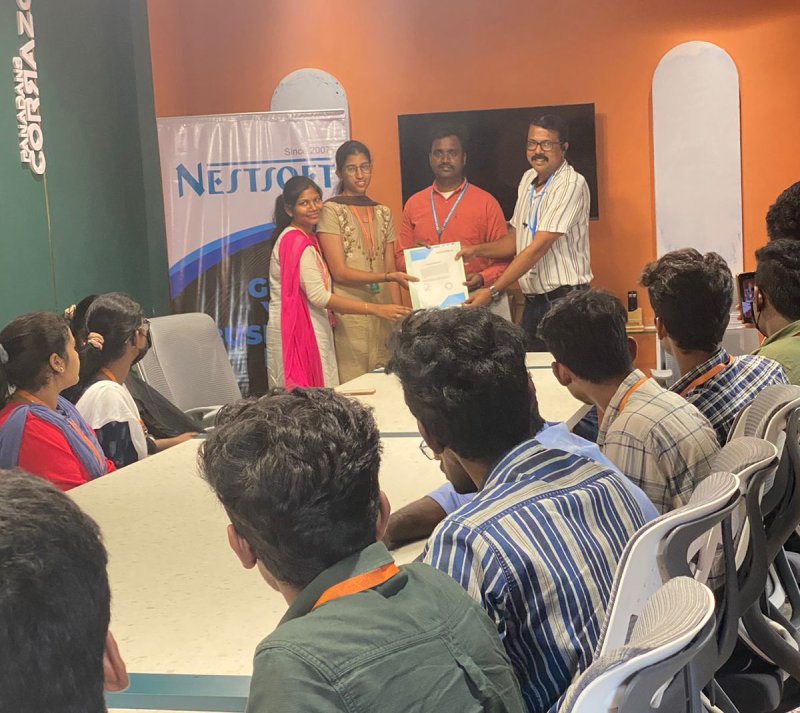
SOC Analyst Training by Experts
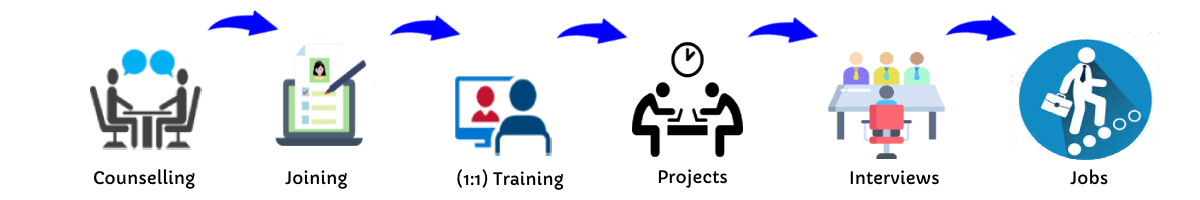
Our Training Process
SOC Analyst - Syllabus, Fees & Duration
Introduction to Cybersecurity
- Basics of cybersecurity
- Common cyber threats and attack vectors
Networking Fundamentals:
- Understanding TCP/IP
- Network protocols
- Firewalls, routers, and switches
Operating Systems
- In-depth knowledge of Windows, Linux, and possibly macOS
- File systems and permissions
Security Technologies
- Antivirus and anti-malware solutions
- Intrusion detection/prevention systems (IDS/IPS)
- Security information and event management (SIEM) systems
Incident Response
- Incident detection and analysis
- Incident classification and escalation
- Incident documentation and reporting
Threat Intelligence:
- Understanding threat intelligence
- Integrating threat intelligence into daily operations
Security Monitoring:
- Log analysis
- Network traffic analysis
- Endpoint security monitoring
Vulnerability Management
'- Identifying and prioritizing vulnerabilities
- Patch management
Security Policies and Compliance
- Understanding security policies and procedures
- Compliance standards and regulations
Hands-on Labs and Simulations
- Practical exercises & simulations for real scenarios
- Use of cybersecurity tools in a controlled environment
Soft Skills
- Communication and collaboration
- Analytical thinking and problem-solving
This syllabus is not final and can be customized as per needs/updates




 Threat Intelligence Analysis:Stay informed about current cyber threats and trends. Additionally, ongoing professional development is often recommended to keep SOC analysts updated on the latest threats and technologies. Network and System Security:Implement and maintain security measures such as firewalls, intrusion detection/prevention systems, and antivirus solutions. Forensic Analysis:Perform forensic analysis on security incidents to understand the scope, impact, and root causes. Here are some common tasks and roles performed by cybersecurity analysts:Monitoring Security Infrastructure:Continuously monitor security alerts and events to identify potential security incidents. Security Awareness Training:Educate employees on security best practices and conduct training sessions to raise awareness about potential cyber threats. The duration of SOC analyst training programs in Taif can vary based on factors such as the depth of content, the training format (full-time, part-time, online, on-site), and the prior experience of participants. Some programs may be intensive, lasting a few weeks, while others may be part-time over several months. They need to stay updated on the latest cyber threats, security technologies, and industry best practices to effectively address the evolving landscape of cybersecurity risks. Some programs may be intensive, lasting a few weeks, while others may be part-time over several months.
Threat Intelligence Analysis:Stay informed about current cyber threats and trends. Additionally, ongoing professional development is often recommended to keep SOC analysts updated on the latest threats and technologies. Network and System Security:Implement and maintain security measures such as firewalls, intrusion detection/prevention systems, and antivirus solutions. Forensic Analysis:Perform forensic analysis on security incidents to understand the scope, impact, and root causes. Here are some common tasks and roles performed by cybersecurity analysts:Monitoring Security Infrastructure:Continuously monitor security alerts and events to identify potential security incidents. Security Awareness Training:Educate employees on security best practices and conduct training sessions to raise awareness about potential cyber threats. The duration of SOC analyst training programs in Taif can vary based on factors such as the depth of content, the training format (full-time, part-time, online, on-site), and the prior experience of participants. Some programs may be intensive, lasting a few weeks, while others may be part-time over several months. They need to stay updated on the latest cyber threats, security technologies, and industry best practices to effectively address the evolving landscape of cybersecurity risks. Some programs may be intensive, lasting a few weeks, while others may be part-time over several months.